Construction compliance is no longer limited to safety manuals and OSHA binders. Today, it includes IT compliance, data protection, and construction cybersecurity requirements that directly impact your ability to bid, win, and deliver projects.
For general contractors and specialty subcontractors, modern compliance centers on three priorities:
- Protecting project and personal data
- Meeting government and owner requirements
- Proving controls are consistently followed across offices, job sites, and subcontractors
If your firm handles government contracts, payment data, employee information, or digital blueprints, cybersecurity in construction is now part of your operational foundation. The question is not whether compliance applies to you. The question is whether you are prepared.
The Core Drivers of Construction Compliance
Government and Defense Contracts
If your firm bids on Department of Defense projects that include CMMC clauses, CMMC compliance is required to be eligible for award.
The Cybersecurity Maturity Model Certification framework, built on NIST SP 800-171, protects Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). In simple terms, CMMC compliance requires defense contractors to implement and maintain documented cybersecurity controls at Levels 1 through 3, depending on contract requirements. If a solicitation requires a certain CMMC level and you do not have it, you generally cannot bid for or win that DoD contract.
A typical CMMC compliance checklist includes access controls, multi-factor authentication, secure configuration management, incident response planning, logging and monitoring, physical security, and ongoing documentation. Many contractors work with a CMMC compliance consultant to close gaps and prepare for assessment.
Data Privacy Laws and State Regulations
Construction firms manage more than blueprints. You also handle HR records, payroll data, vendor banking details, client information, and online payments.
State-level data privacy laws, including the Texas Data Privacy and Security Act, increase regulatory pressure—especially for multi-state contractors. Noncompliance can result in fines, breach notifications, contract disputes, and reputational damage.
Data protection is no longer optional. It is a legal requirement tied directly to construction compliance.
Client-Mandated Cybersecurity Requirements
Owners and institutional clients increasingly include cybersecurity in construction requirements directly in contracts and SLAs.
Common clauses include:
- Mandatory encryption
- Defined breach notification timelines
- Audit rights
- Vendor risk controls
- Secure collaboration requirements
In many agreements, legal responsibility for safeguarding project information shifts to the contractor. If a subcontractor mishandles sensitive data, the prime contractor is often held accountable.
Here is a chart to simplify the data based on each category:
What IT Compliance Looks Like in Construction
IT compliance is not installing antivirus and hoping for the best. It requires formal controls tied to documented policies.
Construction Cybersecurity Baseline
Strong construction cybersecurity starts with clearly defined controls and consistent enforcement. The table below outlines the core security measures every contractor should have in place, what risks they mitigate, and where they must be applied to support IT compliance and audit readiness.
| Cybersecurity Control | What It Protects Against | Must Be Enforced Across |
| Secure Network Architecture | Unauthorized access, network breaches, lateral movement | Corporate offices, job trailers, cloud environments |
| Firewalls & Endpoint Protection | Malware, ransomware, phishing attacks | Office servers, field laptops, remote devices |
| Consistent Patching & Vulnerability Management | Exploited software flaws, zero-day vulnerabilities | All workstations, servers, mobile devices, cloud systems |
| Multi-Factor Authentication (MFA) | Credential theft, account compromise | Email, project management systems, VPN, cloud apps |
| Encryption (At Rest & In Transit) | Data interception, blueprint theft, financial data exposure | File servers, cloud storage, shared project platforms |
| Centralized Logging & Monitoring | Undetected breaches, compliance gaps | Entire network, endpoints, cloud platforms |
| Written Incident Response Plan | Delayed breach response, regulatory penalties | Organization-wide including subcontractor collaboration environments |
If you cannot prove controls are operating, you are not compliant.
NIST 800-171 and CMMC in Practice
For defense-related work, alignment with NIST 800-171 is foundational. These controls govern how contractors protect CUI within their environments.
Requirements include:
- Limiting system access to authorized users
- Monitoring and logging activity
- Securing system configurations
- Performing regular self-assessments
- Maintaining evidence of compliance
CMMC builds on these controls and introduces structured certification. Unlike informal self-attestation, CMMC compliance often requires formal review and third-party validation.
This is where documentation becomes critical. A compliance IT audit will not rely on verbal assurances. Auditors expect policies, procedures, screenshots, logs, and historical records.
The Biggest Pain Points in Construction IT Compliance
Legacy and Fragmented Systems
Many contractors operate with:
- Aging on-premise servers
- Disconnected file-sharing systems
- Standalone accounting tools
- Limited centralized monitoring
These environments were not designed for modern construction cybersecurity or compliance IT audit requirements. Retrofitting them can be costly and complex.
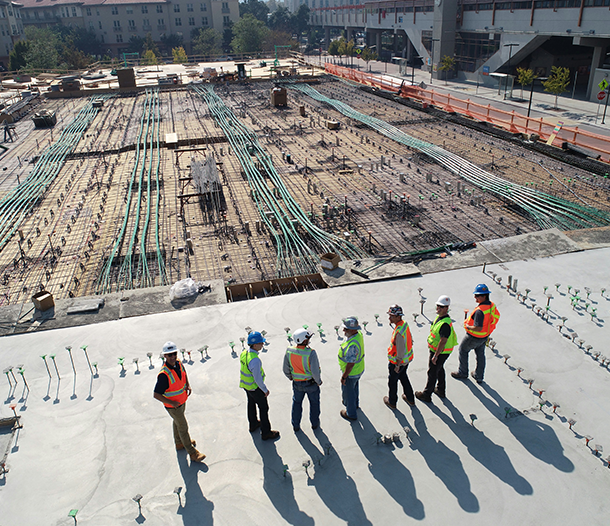
Distributed Job Sites and Mobile Teams
Construction does not happen in a single building.
Field crews use:
- Tablets and laptops in job trailers
- Public or mobile Wi-Fi
- Cloud apps from multiple devices
Without centralized enforcement, you get:
- Inconsistent patching
- Weak password practices
- Data stored locally on unsecured devices
- Gaps in monitoring
Each job site becomes a potential vulnerability in your construction compliance posture.
Subcontractor and Vendor Risk
Projects involve dozens of subcontractors. Each may access shared drawings, BIM models, and payment systems.
If one subcontractor experiences a breach, your firm may still be contractually liable.
Managing subcontractor risk requires:
- Security questionnaires
- Minimum cybersecurity standards
- Secure file-sharing platforms
- Documented oversight procedures
Without structure, vendor risk becomes the weakest link in your cybersecurity in construction strategy.
Documentation and Audit Readiness
A major compliance obstacle is documentation.
Firms often struggle with:
- Writing formal IT policies
- Maintaining asset inventories
- Tracking system updates
- Capturing control evidence
- Preparing for a compliance IT audit
Construction compliance is not a one-time project completed before a major bid. It is an ongoing program that requires continuous monitoring and documentation updates.
How Managed IT Services Support Construction Compliance
Most mid-market contractors do not employ full-time compliance officers or cybersecurity specialists. That is where managed IT services for construction play a critical role.
An experienced provider can help with:
- Gap assessments against NIST 800-171
- Building a CMMC compliance checklist
- Policy development and documentation
- Continuous monitoring and logging
- Secure cloud migration
- Backup testing and ransomware protection
- Subcontractor risk oversight
For firms in North Texas, managed IT services Dallas providers and specialized IT services Dallas firms can deliver localized support while aligning systems with federal and state compliance requirements.
The right partner does more than maintain servers. They help you:
- Eliminate bid-blocking compliance gaps
- Protect blueprints and bids from ransomware
- Maintain audit-ready documentation
- Adapt to evolving data privacy laws
Conclusion
Construction compliance is not just a regulatory burden. It is a competitive advantage that directly impacts revenue and growth.
When your firm can clearly demonstrate CMMC compliance, alignment with NIST 800-171, strong construction cybersecurity controls, and adherence to data privacy laws, you become a lower-risk partner for government agencies and enterprise clients.
Cybersecurity in construction is not only about avoiding penalties. It protects bidding eligibility, safeguards intellectual property, and strengthens client trust.
IT compliance is now part of how modern contractors win larger contracts and scale confidently. If your compliance program is reactive or undocumented, now is the time to strengthen it before it costs you your next opportunity.