
Scale Up. We Keep Momentum.
You signed a new lease on a second location. Your team doubled. You landed that enterprise client who requires 24/7 uptime and a

You signed a new lease on a second location. Your team doubled. You landed that enterprise client who requires 24/7 uptime and a

Your warehouse never stops moving. Forklifts, inventory scans, shift handoffs, shipping systems — all of it running on a network that was probably

A lot of property management companies are running the same basic security setup they’ve had for years: antivirus on the office computers, maybe

When something breaks in one of your buildings, such as an HVAC unit, a roof section, a parking gate, you call a vendor.

Property management is a demanding business. You’re overseeing operations across multiple locations, managing vendors, keeping tenants happy, and protecting asset value. IT is

It’s a scenario most property managers don’t think about until it’s too late. A tenant calls. Their network was compromised. Customer data, financial

Managing one property is complex. Managing five, ten, or twenty? The complexity doesn’t just add up, it multiplies. And somewhere inside that complexity,

Ask any property manager what tenants complain about most, and the answer used to be parking, HVAC, or the coffee in the lobby.
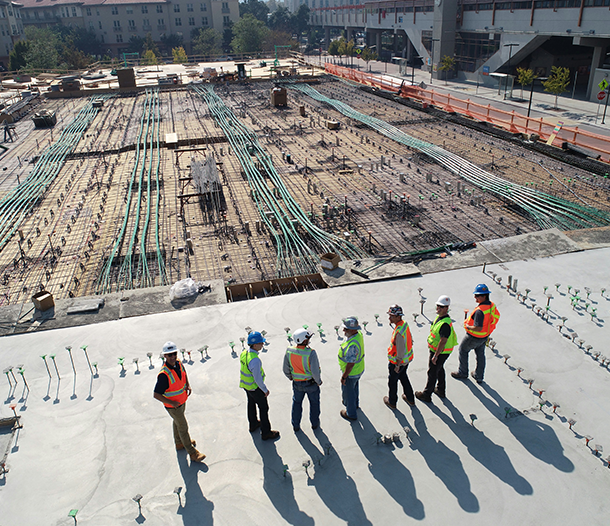
Every construction project starts with a plan: a timeline, a budget, a crew, and a clear scope. But somewhere between breaking ground and